8 blockchain security issues you are likely to
Content
A typical collision attack happens when two separate inputs have the same hash value. An adversary can make a false top-up attack if they successfully make an untruthful transfer. The time-locked transaction manipulation occurs when one party has padlocked some tokens for a specified time. This attack Cryptocurrency Exchange Security is low severity because the hacker can only do a few significant exploits. Avoiding the Merkle-Damgard construction for hash functions is an efficient prevention mechanism. This attack is carried out when an adversary can successfully calculate the length of a hash.
- This means that even if one node is compromised, the data remains secure and inaccessible to unauthorised users.
- Further research into measuring the performance of the various mitigation strategies suggested in this paper will help blockchain developers create more resilient solutions.
- Both attack methods compromise information stored on the blockchain and undermine trust.
- The attacker mines a block stealthily and sends the unconfirmed transaction to the other node, possibly to a merchant node.
- In fact, it’s much harder for bad actors to pull off a 51% attack on a public blockchain than on a private one.
4. Quantum-Resistant Cryptography?
Hackers breached the Ronin Network and made off with around $625 million Cryptocurrency wallet worth of Ether and USDC (a stablecoin). Investigators said that a North Korean state-backed hacking collective, the Lazarus Group, was linked to the theft. Sky Mavis (Axie Infinity’s developer) recovered $5.7 million of the stolen funds a month later, but it remains the largest cryptocurrency hack in history. Ever since Bitcoin came on the scene in 2009, we’ve been steadily getting there with systems already in production that can withstand high levels of attack and abuse. But, like any new technology, it still requires a lot of expertise to build, deploy and operate blockchain securely.
Typical vulnerabilities and bridge security in blockchain technology
The report stated that the technology is nascent, hence featuring many vulnerabilities that hackers routinely exploit. Excluding its initial application in cryptocurrency, https://www.xcritical.com/ it’s currently getting used in property, healthcare, smart contracts and many other fields. Blockchain technology has revolutionized and redefined the way we establish trust and conduct secure transactions in the digital age. Despite the inherent security concepts of blockchain, it’s not immune to threats. To tackle this blockchain security issue, use malicious link detection software to prohibit nodes from honoring cross-domain access. They only know the interface to utilize the product or service on blockchain technology.
A. Overview of Global Regulations Related to Blockchain:
They do this by amassing low-cost, out-of-the-money put options and engaging in short futures contracts. Subsequently, they carry out double-spending transactions, overwhelming network nodes, or redirecting hashing power to an alternative SHA-256 protocol. For those who wield influence within the cryptocurrency community, there could be proposals for a contentious fork, possibly with the collaboration of developers with ulterior motives.
KnowBe4 Launches AI Agents to Counter Phishing Threats
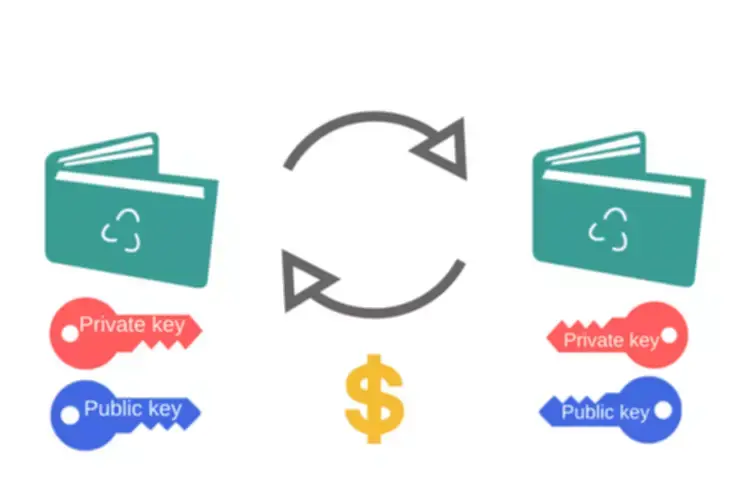
Only users with appropriate credentials can access blockchains, and everyone else remains locked out. Finally, audit network security issues that govern access to blockchain networks. For instance, consider device security, password hygiene, and access management. Training is also important, as one careless employee can open the way to 51 attack methods. These digital wallets require more than one user to approve blockchain network operations, essentially a form of separation of duties.

In 2024, reports emerged about the arrest of a SIM card swapping ring that gained access to an FTX employee’s accounts and siphoned off millions in crypto. Coincheck survived the hack and continued operating despite being bought out a few months later by the Japanese financial services company Monex Group. The amount of cryptocurrency stolen from exchanges and other platforms in 2023, down from 2022’s $3.8 billion.
Blockchain governance and access control are essential for maintaining the integrity and security of blockchain networks. At Rapid Innovation, we guide our clients in establishing effective governance frameworks and access control mechanisms tailored to their specific needs. Blockchain security is important because it helps protect the data and transactions stored on the blockchain. It also helps to ensure that the blockchain is not susceptible to attacks from hackers. It is, therefore, essential that blockchain security is taken seriously by companies that use this technology. Several measures can be taken to improve security, such as using multiple layers of security, encrypting data, and using digital signatures.
Blockchains can put sensitive data at risk, resulting in significant financial losses or data exposure. Companies adopting private or public blockchain solutions should thoroughly assess their security vulnerabilities. Private blockchain security ensures control and confidentiality for the blockchain owner, making it suitable for many enterprise uses. Attackers can also exploit centralized chains, using the blockchain controller as an attack vector. Public blockchain technology is decentralized, with no single controlling entity.
IAM solutions define who can use private keys and change the blockchain ledger. Unauthorized users are blocked at the source, making it harder to launch insider attacks. Blockchain technology is a decentralized and distributed digital ledger system that records transactions across a network of computers, ensuring transparency, security, and immutability of data.
Its applications are diverse and impactful, providing innovative solutions to some of the most pressing challenges faced by organisations today. By leveraging blockchain for threat intelligence, organisations can create a reliable repository of information that is resistant to tampering. This not only enhances the quality of the intelligence gathered but also fosters collaboration among organisations, as they can share insights with confidence in the data’s integrity.
This information helps the testing team to understand the blockchain network’s functionality and business requirements. A blockchain network that functions within a confined setting, like a closed network or under the management of a single entity, is classified as a private blockchain. Despite operating similarly to a public blockchain by utilizing peer-to-peer connections and decentralization, this type of blockchain operates on a much smaller scale. Private blockchains are typically run on a limited network within a company or organization, and participation and computing power are typically restricted to authorized individuals. However, this does not mean that blockchain is not vulnerable to cyber-attacks and security fraud.
Blockchain is predicated on the concepts of consensus, decentralization and cryptography to confirm dealings trust. However, several blockchain security problems have arisen thanks to faulty technology implementation. In this series, we have delved into the potential risks that blockchain technologies, such as those based on Ethereum, present for corporate entities. On this note, the founding team or community of each blockchain network are now aware that the issue of blockchain security is vital.
Let us help you navigate the evolving landscape of cybersecurity, including the latest cyber attack trends, and ensure your systems remain secure and resilient. Additionally, the integration of blockchain in security applications and the development of blockchain security companies are crucial for addressing vulnerabilities. As we explore the intersection of blockchain and cyber security, it is essential to consider the role of encryption in securing blockchain data, as well as the advancements in hardware wallet blockchain solutions. Furthermore, the rise of crypto audits and the involvement of organizations like Certik Skynet and Fireblocks crypto underline the growing need for comprehensive security measures in the blockchain ecosystem.
At Rapid Innovation, we are committed to helping our clients implement best practices in security to mitigate risks and enhance their blockchain solutions. By leveraging our expertise, you can achieve greater ROI while ensuring the safety and integrity of your blockchain applications. Our comprehensive approach includes thorough audits, adherence to best practices, and the use of established libraries, ensuring that your smart contracts are robust and reliable.
